HIPAA Security Rule Explained
A comprehensive guide to implementing the administrative, physical, and technical safeguards required by the HIPAA Security Rule.
Article by
HIPAA Guidelines Editorial TeamThe HIPAA Security Rule sets national standards for protecting electronic protected health information (ePHI). It requires covered entities and business associates to implement three categories of safeguards.
Administrative Safeguards
Administrative safeguards are the policies and procedures that manage the selection, development, implementation, and maintenance of security measures. Key requirements include:
- Security Management Process — Conduct risk analyses to identify threats and vulnerabilities
- Workforce Security — Ensure authorised personnel have appropriate access to ePHI
- Information Access Management — Implement access authorisation and modification policies
- Security Awareness Training — Train all workforce members on security policies and procedures
- Contingency Planning — Develop plans for responding to emergencies that affect ePHI systems
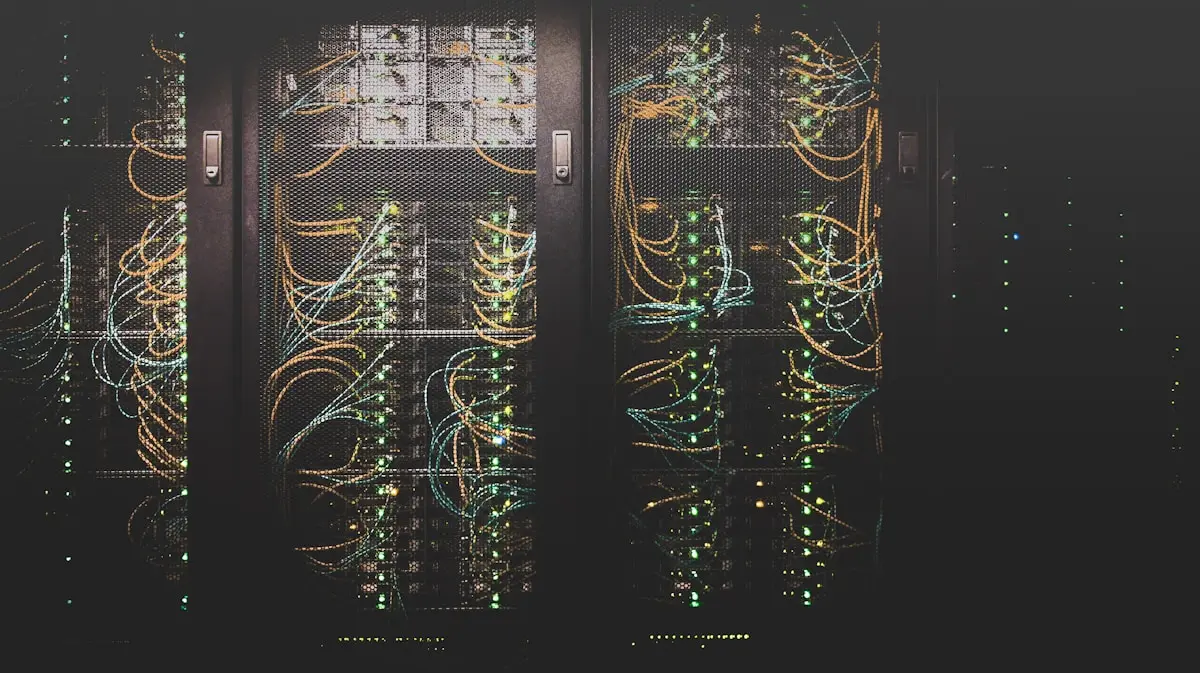
Physical Safeguards
Physical safeguards protect the physical access to ePHI systems and facilities:
- Facility Access Controls — Limit physical access to areas where ePHI is stored
- Workstation Security — Restrict access to workstations that process ePHI
- Device and Media Controls — Govern the receipt, movement, and disposal of hardware and electronic media
Technical Safeguards
Technical safeguards are the technology and related policies that protect ePHI and control access to it:
- Access Control — Unique user identification, emergency access procedures, automatic logoff
- Audit Controls — Hardware, software, and procedural mechanisms that record and examine activity
- Integrity Controls — Ensure ePHI is not altered or destroyed in an unauthorised manner
- Transmission Security — Guard against unauthorised access to ePHI being transmitted over networks
Implementation Approach
When implementing Security Rule safeguards, organisations should:
- Conduct a thorough risk analysis
- Develop a remediation plan based on identified risks
- Implement safeguards proportionate to the risk level
- Document all policies and procedures
- Review and update regularly
Encryption and Authentication
While not all safeguards are required, encryption of ePHI at rest and in transit is strongly recommended. Multi-factor authentication adds an additional layer of security beyond passwords.
Addressable vs Required
The Security Rule distinguishes between required and addressable implementation specifications. Required specifications must be implemented. For addressable specifications, the entity must assess whether the safeguard is reasonable and appropriate, and if not, document why and implement an equivalent alternative.
Understanding these three safeguard categories is essential for any organisation handling electronic health information.
Further Reading
- conduct a thorough HIPAA risk assessment
- HIPAA training requirements for workforce members
- HIPAA compliance checklist
Article by
HIPAA Guidelines Editorial TeamThe editorial team at HIPAA Guidelines researches and writes authoritative guides on HIPAA compliance, privacy regulations, and healthcare data protection.
Related Articles
What Is the HIPAA Privacy Rule?
Learn the fundamentals of the HIPAA Privacy Rule and how it protects patient health information.
HIPAA Breach Notification Rule Requirements
Understanding when and how to report breaches of unsecured protected health information under HIPAA.
